We first get our target IP address using arp-scan

Then run a simple nmap scan

We did not get much info from that so now gotta check whats on port 80 and there we find a webpage with two cats and some text that implies they are somehow different

So I downloaded both of them to check that using their md5 hashes

And as we can see next they are indeed different

After testing what’s listed here on cat-hidden.jpg i managed to find out that it is protected by a password so we can try to bruteforce it using steghide or stegseek, I chose stegseek because it’s way faster

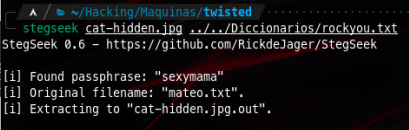
After inspecting the output we get a file which content seems as a password, also we know that the original file name was mateo.txt which can be a possible username. At this point we got a pair of possible credentials so we can try to log into ssh on port 2222

Also using this same method for cat-original.jpg we found another pair of possible credentials, we will check them later


Now we are in! Time to begin our privilege escalation. Starting enumeration I found a note in mateo’s home directory with a path to an audio file, this file is available on the website so we can simply download it using wget


It was a morse audio. I found this tool online that decodes morse audio files to text and got a rather weird message 😅😅

I was not able to find anything else with mateo’s user so I will switch to markus using su with the password I found earlier

There was a note from Markus mentioning an id_rsa file from bonita. If I try to read if using cat I get a permission denied error

But fortunately I noticed that /usr/bin/tail has CAP_DAC_READ_SEARCH capability (thank you LinPeas!) and according to HackTricks we can use this to bypass read restrictions
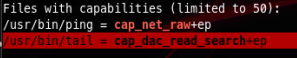


Now that we read and saved this id_rsa we can save and use it to log into bonita’s user to get our user.txt

At this point we can also get our root flag using tail but what’s the fun in that? We want to root it! 😆😆 So I am going to download beroot file and analyze it using ghidra


And after analyzing the source code we found the 4 digit pass for the file

And we successfully rooted this machine!
